What should the security features of an application provide?

.
Subsequently, one may also ask, what is application security and why is it important?
To protect users and data, application security has become an important consideration for businesses globally. When it comes to creating and releasing an app, developers must continually monitor, fix and prevent security vulnerabilities.
Beside above, how does application security work? Application security is the process of making apps more secure by finding, fixing, and enhancing the security of apps. Much of this happens during the development phase, but it includes tools and methods to protect apps once they are deployed.
In this manner, what is application level security?
Application level security refers to those security services that are invoked at the interface between an application and a queue manager to which it is connected. Application level security is illustrated in Figure 1. Application level security is also known as end-to-end security or message level security.
What are three steps you should take to ensure your security when using apps?
8 Important Steps To Secure Your Mobile App
- STEP 1 – Secure the source code.
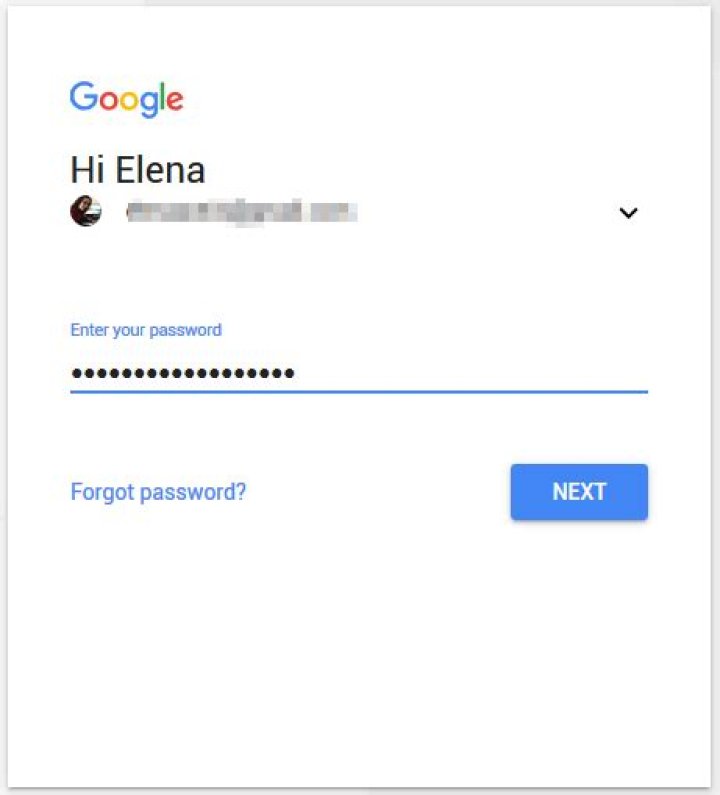
- STEP 2 – Have security measures to protect data and deny unauthorized access.
- STEP 3 – Identifications, Authentication, and Authorization.
- STEP 4 – Activate a good mobile encryption policy.
- STEP 5 – Implement a strong API security strategy.
What are the three types of security?
Principle 8: The Three Types of Security Controls Are Preventative, Detective, and Responsive. Controls (such as documented processes) and countermeasures (such as firewalls) must be implemented as one or more of these previous types, or the controls are not there for the purposes of security.What do you mean by application security?
Application security is the general practice of adding features or functionality to software to prevent a range of different threats. These include denial of service attacks and other cyberattacks, and data breaches or data theft situations.What is application level?
The application level refers to the applications that sit on top of the network and use the networks to get their data from one endpoint to another—such as a server.What is application shielding?
Application shielding refers to a set of technologies that modify an application's source, byte or binary code, to make the application more resistant to intrusion, tampering and reverse engineering. Enterprises shield their applications to protect the organization's software-based assets.How do you test security on an application?
Components of Veracode's testing solutions include:- Black box analysis. Veracode Web Application Scanning provides dynamic analysis security testing tools that help to identify vulnerabilities in applications running in production.
- White box analysis.
- Third-party software analysis.
- Manual penetration testing.
What are the 3 principles of information security?
A principle which is a core requirement of information security for the safe utilization, flow, and storage of information is the CIA triad. CIA stands for confidentiality, integrity, and availability and these are the three main objectives of information security.How do I secure an application?
Let's start with number one.- Follow the OWASP Top Ten. I've already covered this in greater depth, in a recent post.
- Get an Application Security Audit.
- Implement Proper Logging.
- Use Real-time Security Monitoring and Protection.
- Encrypt Everything.
- Harden Everything.
- Keep Your Servers Up to Date.
- Keep Your Software Up to Date.
What is application system?
Application System - Defined An application system normally consists of a user interface, business logic and a database of some sort. The user interface is something that you can see and something that is used to interact with the computer. Most large computer systems use multiple computer languages.What are application security risks?
Here, and for the sake of brevity, I am going to describe the 5 most critical security risks in the list.- SQL injection.
- Sensitive data exposure.
- Broken authentication and session management.
- Cross-Site Scripting (XSS)
- Broken access control.
What is mean security?
Security means safety, as well as the measures taken to be safe or protected. Often this word is used in compounds such as a security measure, security check or security guard. The security department in a business is sometimes just called security.What is the purpose of Owasp?
OWASP (Open Web Application Security Project) is an organization that provides unbiased and practical, cost-effective information about computer and Internet applications.How do I keep my phone secure?
Read on for six easy ways to keep your Android phone secure, starting with- Lock your phone (if you haven't already)
- Locate and wipe your phone remotely.
- Let Android scan and verify your apps.
- Keep your phone updated.
- Turn on Chrome's Safe Browsing feature.
How can you protect your personal devices?
How to Protect Your Privacy on Your Mobile Devices- Use a Passcode. This may sound obvious, but according to a Consumer Reports survey, 64% of us don't use our passcodes.
- Be Selective With Your Apps.
- Don't Click on Suspicious Links.
- Enable Remote Wiping.
- Keep Software Up to Date.
- Use Security Applications.
- Stay Off of Open Wi-Fi Networks.
- Write Down Your IMEI.
How do you keep your phone safe and secure?
10 tips to keep your phone safe and secure- Use strong lock screen security.
- Lock your apps.
- Log out of apps and services.
- Use a password manager.
- Use antivirus.
- Don't jailbreak or use unofficial app stores.
- Avoid public networks.
- Encrypt your communications.
How can I protect my mobile data?
Ways to stay secure- Lock your phone with a password or fingerprint detection.
- If it's not already the default on your phone, consider encrypting your data.
- Set up remote wipe.
- Back up phone data.
- Avoid third-party apps.
- Avoid jailbreaking your iPhone or rooting your Android.
- Update operating systems often.
What https means?
Hypertext Transfer Protocol SecureHow do I protect my mobile apps?
5 ways to secure your mobile apps- Secure the code. Mobile malware often exploits bugs in the design or code of an application.
- App Authentication. Ideally an app taking any sort of user information should have authentication.
- Data encryption.
- Alert the user.
- 2-step authentication.
How do I develop an app?
The 9 steps to make an app are:- Sketch your app idea.
- Do some market research.
- Create mockups of your app.
- Make your app's graphic design.
- Build your app landing page.
- Make the app with Xcode and Swift.
- Launch the app in the App Store.
- Market your app to reach the right people.
How do you secure an app name?
How to Reserve an App Name- Login to your itunesconnect.apple.com account.
- Go to My Apps in the top right corner.
- Add new app.
- Complete info for the new app. Note: you will need to have an app bundle to complete it.
- Press “Create” and your app name is now reserved!