What is wardriving and Warchalking?
.
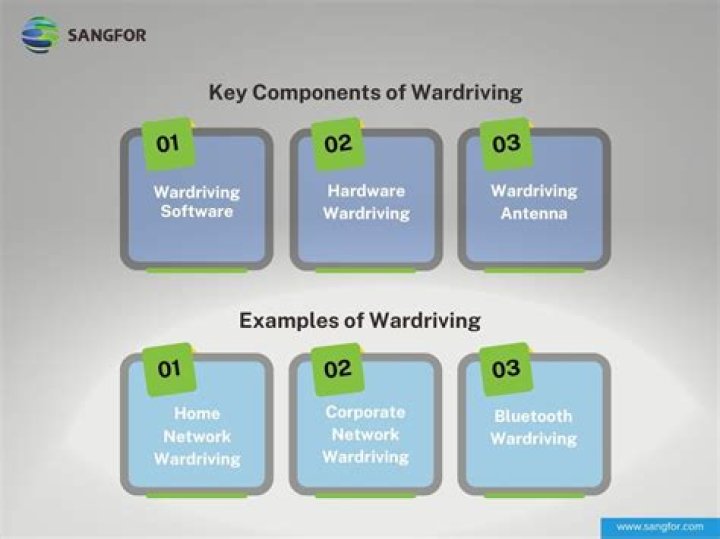
Accordingly, what does wardriving mean?
Wardriving is the act of searching for Wi-Fi wireless networks by a person usually in a moving vehicle, using a laptop or smartphone.
Furthermore, what is the difference between war driving and war chalking? War driving is the hobby of popping in a car and cruising around with a Wi-Fi–equipped laptop looking for open Wi-Fi nodes. War chalking is the act of using specific chalk markings, usually on a sidewalk, to identify Wi-Fi hotspots.
Also asked, what is the purpose of wardriving?
The goal of wardriving may be to find a single usable Wi-Fi network or it may be to map all Wi-Fi signals within a specific area. The latter is also called "access point mapping." While the act of wardriving itself may not be malicious, the data can be used to publicize and/or exploit open or unsecure networks.
What is war driving or war flying?
The act of war driving itself is simply going around looking for wireless networks. This activity is also called access point discovery, LAN-Jacking, WLAN mapping, etc. Some people have also coined the terms War Walking and War Flying by walking or flying around looking for APs.
Related Question AnswersHow can wardriving affect you?
What are the dangers of wardriving? When hackers find open Wi-Fi, they can then place malicious programs onto the network or look through your private data. When attacking a home network, thieves could steal your name and passwords, your Social Security Number, your bank and credit card information, and much more.What is WiFi piggybacking?
Piggybacking on Internet access is the practice of establishing a wireless Internet connection by using another subscriber's wireless Internet access service without the subscriber's explicit permission or knowledge.What is WPS button?
Wi-Fi Protected Setup (WPS) is a feature supplied with many routers. It is designed to make the process of connecting to a secure wireless network from a computer or other device easier. IMPORTANT for Android TV™ models.Can a WiFi signal be boosted?
You can slightly boost your wireless signal by elevating the router above the floor level. WiFi signals radiate outward in all directions, not just horizontally. When your router is on the floor, it's ability to emit strong signals is severely limited.Is packet sniffing detectable?
If the system runs the sniffer, its interface will be in promiscuous mode. The test works like this: Send a ping with the correct IP address into the network but with a wrong mac address. the sniffing host does the sniffing with an interface that has TCP/IP enabled, and thus is able to answer the ICMP packet.What is a rogue wireless device?
A wireless networking term used to describe unauthorized devices connected to the network that poses a significant risk to the organization. Rogue wireless devices can be broken down into two categories: access point (AP) based threats (rogue access points) and computer based threats (rogue peers).What is rogue AP detection?
A Rogue AP is an access point that has been installed on a secure network without explicit authorization from a system administrator. The Rogue AP Detection page displays information about all access points detected by the AP541N in the vicinity of the network.What is an evil twin access point?
An evil twin is a fraudulent Wi-Fi access point that appears to be legitimate but is set up to eavesdrop on wireless communications. The evil twin is the wireless LAN equivalent of the phishing scam.What is NetStumbler used for?
NetStumbler (also known as Network Stumbler) is a tool for Windows that facilitates detection of Wireless LANs using the 802.11b, 802.11a and 802.11g WLAN standards. It runs on Microsoft Windows operating systems from Windows 2000 to Windows XP.How did wardriving get its name?
The name of "wardriving" is often misunderstood. "Wardriving" is the act of searching for Wi-Fi networks. This term derives from the term "wardialing", when modems were used to connect networks a long time ago.What is WiGLE WiFi?
WiGLE, or (Wireless Geographic Logging Engine), is a website for collecting information about the different wireless hotspots around the world. Users can register on the website and upload hotspot data like GPS coordinates, SSID, MAC address and the encryption type used on the hotspots discovered.What risks are associated with wireless communication?
Risks related to wireless WiFi networks (802.11 or Wi-Fi)- Lack of security. Radio waves intrinsically have the power to propagate in all directions, with a relatively wide range.
- War-driving.
- Security risks.
- Data interception.
- Network intrusion.
- Radio jamming.
- Denial of service.
What are the four major threats to the security of wireless networks?
There are a number of main threats that exist to wireless LANS, these include:- Rogue Access Points/Ad-Hoc Networks.
- Denial of Service.
- Configuration Problems (Mis-Configurations/Incomplete Configurations)
- Passive Capturing.



