A token is used to make security decisions and tostore tamper-proof information about some system entity. While atoken is generally used to represent only securityinformation, it is capable of holding additional free-form datathat can be attached while the token is beingcreated..
Also, what is a token used for?
A security token is a physical device usedto gain access to an electronically restricted resource. Thetoken is used in addition to or in place of apassword. It acts like an electronic key to accesssomething.
Subsequently, question is, what is an account token? An access token is an object that describes thesecurity context of a process or thread. The information in atoken includes the identity and privileges of the useraccount associated with the process or thread. If thepassword is authenticated, the system produces an accesstoken.
how does the token work?
Tokens. A token is a device that employsan encrypted key for which the encryption algorithm—themethod of generating an encrypted password—is known to anetwork's authentication server. There are both software andhardware tokens.
What is a token worth?
Token money has less commodity valuecompared to its face value. Token money is also moneywhose face value exceeds its cost of production, i.e. theintrinsic value is lower than the extrinsic value.This means that the actual worth of a note or coin is muchless than what we use it for.
Related Question Answers
What do you mean by token?
In general, a token is an object that representssomething else, such as another object (either physical orvirtual), or an abstract concept as, for example, a gift issometimes referred to as a token of the giver's esteem forthe recipient. In computers, there are a number of types oftokens.How does a token work?
The RSA SecurID authentication mechanism consists of a"token" — either hardware (e.g. a key fob) or software(a soft token) — which is assigned to a computer userand which creates an authentication code at fixed intervals(usually 60 seconds) using a built-in clock and the card'sfactory-encoded almost random key (How is a token generated?
Once an Access Token has been generated,the token can be used to authorize individual requests madeby your users as they are passed to your application. Yourapplication will validate the token sent along with eachrequest. Both Access and Refresh tokens can be revoked(independently, or together).How can I generate authorization token?
To set the authorization parameters for a request, you havethree options: - Click the Get New Access Token button.
- In the "Access Token" field, enter a token, or an environmentdefined variable, and click the Send button.
- In the "Available Tokens" drop down menu, select an existingtoken and click the Send button.
What are the different types of tokens?
C tokens are of six types. They are, - Keywords (eg: int, while),
- Identifiers (eg: main, total),
- Constants (eg: 10, 20),
- Strings (eg: “total”, “hello”),
- Special symbols (eg: (), {}),
- Operators (eg: +, /,-,*)
How do I access token?
To obtain an 'App' Access Token from Facebook (which neverexpires) just follow the steps below. - 1) Go to developers.facebook.com and click on Log In in the topright.
- 2) If this is your first time signing in to the FacebookDeveloper portal then click on Register.
- 3) Accept the Facebook terms and click Next.
Why do we need token based authentication?
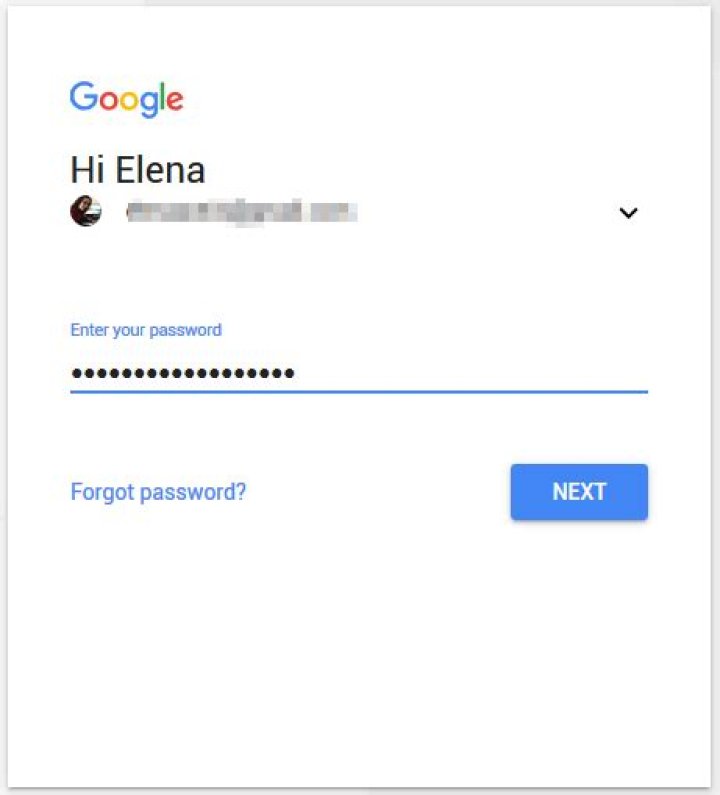
Token is used to assure the authenticity of theuser. The Token-Based Authentication works asFollows: A user enters the name and password into the client(client means the browser or mobile devices etc). The client thensends these credentials (i.e. username and password) to theAuthorization Server.How do OTP tokens work?
The use of one-time password tokens hardens atraditional ID and password system by adding another, dynamiccredential. Depending upon the vendor, an OTP token willgenerate a PIN synchronously or asynchronously. Synchronoustokens use a secret key and time to create aone-time password.How does soft token work?
A soft token is a software-based securitytoken that generates a single-use login PIN. Softtokens are an attempt to replicate the security advantages ofmultifactor authentication, while simplifying distribution andlowering costs. A smartphone soft token app performs thesame task as a hardware-based security token.How does Gemalto token work?
The RSA SecurID authentication mechanism consists of a"token" — either hardware (e.g. a USB dongle) orsoftware (a soft token) — which is assigned to acomputer user and which generates an authentication code at fixedintervals (usually 60 seconds) using a built-in clock and thecard's factory-encoded random key (What is OAuth and how it works?
OAuth doesn't share password data but insteaduses authorization tokens to prove an identity between consumersand service providers. OAuth is an authentication protocolthat allows you to approve one application interacting with anotheron your behalf without giving away your password.What is use token?
You should also know the most common uses forboth coins and tokens. Coins are most often used simply asmoney; however, some coins do have other uses. These includebeing used to fuel applications, being used as a stake to validatetransaction on a network, or being used to fuel smart contract andtoken transactions.What is difference between coin and token?
Coins are currencies that can be used forbuying and selling things. You can buy a token with a coin,but not vice versa. Coin operates independently, whiletoken has a specific use in the project'secosystem.What is authorization bearer token?
Bearer authentication (also called tokenauthentication) is an HTTP authentication scheme thatinvolves security tokens called bearer tokens. Theclient must send this token in the Authorizationheader when making requests to protected resources:Authorization: Bearer<token>How do disconnected tokens work?
Disconnected tokens are not linked to thecomputer or network in any way; rather, the user enters theinformation from the token manually into the system.Connected tokens work electronically and automaticallytransmit information to the network once they'reconnected.How does a Digipass work?
With a single press of the button, Digipass GO 6displays a dynamic one-time password for each time a user remotelylogs into an application, website or network. Digipass GO 6is a 'one-button' authenticator to effectively combat internetfraud by replacing static or paper-based passwordsystems.How do authenticators work?
Time-based One-time Password (TOTP), popularized mainlyby Google Authenticator, verifies your identity based on ashared secret. This secret must be shared online between you andthe provider. When logging into a website, your device generates aunique code, based on the shared secret and the currenttime.What does token code mean?
A token is a small device issued by banks totheir customers for generating a unique security code fortheir online money transfers. A token has to be linked toyour account and activated before you can use it. But sometimespeople don't know how to walk through the process of activatingtheir tokens.What is OAuth token?
OAuth (Open Authorization) is an open standardfor token-based authentication and authorization on theInternet. OAuth, which is pronounced "oh-auth," allows anend user's account information to be used by third-party services,such as Facebook, without exposing the user'spassword.