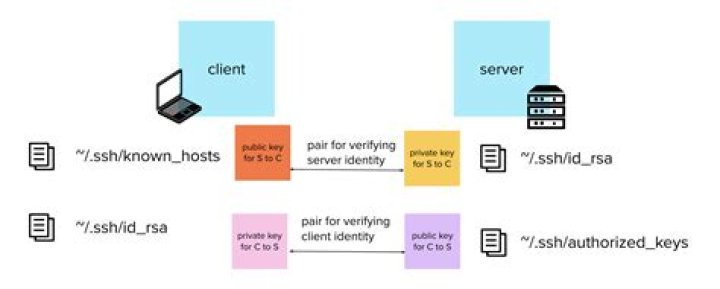
What is the difference between Known_hosts and Authorized_keys?
.
Also question is, what is in Known_hosts?
The known_hosts file is for verifying the identity of other systems. ssh(1) can automatically add keys to the user's file, but they can be added manually as well. The file contains a list of public keys for all the hosts which the user has connected to.
can I delete Known_hosts file? Method Two — Deleting your known_hosts file If you log in to other servers, do not delete the known_hosts file, or you'll have no way of knowing if your SSH keys have changed. Delete your entire known_hosts file (on your local computer) if you have several hosts that need to be updated.
Likewise, people ask, what is stored in Authorized_keys?
Authorized_keys File in SSH. The authorized_keys file in SSH specifies the SSH keys that can be used for logging into the user account for which the file is configured. It is a highly important configuration file, as it configures permanent access using SSH keys and needs proper management.
What is difference between private and public SSH?
Private key stays with the user (and only there), while the public key is sent to the server. Typically with the ssh-copy-id utility. Server stores the public key (and "marks" it as authorized). Server will now allow access to anyone who can prove they have the corresponding private key.
Related Question AnswersWhat is Ssh_host_rsa_key?
ssh_host_rsa_key — The RSA private key used by the sshd daemon for version 2 of the SSH protocol.What is Hostkey?
A host key is a cryptographic key used for authenticating computers in the SSH protocol. Host keys are key pairs, typically using the RSA, DSA, or ECDSA algorithms. Public host keys are stored on and/or distributed to SSH clients, and private keys are stored on SSH servers.What is Sshhostkeyfingerprint?
A host key fingerprint is also known as RSA key, host key, and key fingerprint. Every SSH server is configured to use a host key to verify that the client is connecting to the correct host. The SSH server administrator provides the host key fingerprint to the various clients.What is Ecdsa key?
ECDSA (Elliptical curve Digital Signature Algorithm) is an Elliptic Curve implementation of DSA (Digital Signature Algorithm). Elliptic curve cryptography is able to provide the relatively the same level of security level as RSA with a smaller key.What is the use of Authorized_keys?
authorized_keys is used to identify which public keys are used to match to a users private key to authenticate to the targeted ssh system. The known_hosts is used from the source system to identify the target system's authenticity.Where is Filezilla host key?
5 Answers. If you use the standard openssh console client (cygwin or from linux), host keys are stored, one-per-line, in ~/. ssh/known_hosts. From there, it's a simple matter of figuring out which bit of that host key is needed for your library.Where is the SSH key stored?
By default, the keys will be stored in the ~/. ssh directory within your user's home directory. The private key will be called id_rsa and the associated public key will be called id_rsa.Where are public keys stored?
Public-Key Basics By default, the private key is stored in ~/. ssh/id_rsa and the public key is stored in ~/. ssh/id_rsa. When you authenticate to a server using public-key authentication, the SSH client offers a copy of the public key to the server and the server then compares it against the keys listed in your ~/.What does SSH stand for?
Secure ShellWhat is SSH port?
Secure Shell (SSH) is a cryptographic network protocol for operating network services securely over an unsecured network. The standard TCP port for SSH is 22. SSH is generally used to access Unix-like operating systems, but it can also be used on Microsoft Windows. Windows 10 uses OpenSSH as its default SSH client.What is SSH public key?
SSH public-key authentication relies on asymmetric cryptographic algorithms that generate a pair of separate keys (a key pair), one "private" and the other "public". You keep the private key a secret and store it on the computer you use to connect to the remote system.What do you mean by public key?
Definition - What does Public Key mean? A public key is created in public key encryption cryptography that uses asymmetric-key encryption algorithms. Public keys are used to convert a message into an unreadable format. Decryption is carried out using a different, but matching, private key.What is SSH key pair?
Understanding SSH Key Pairs. The SSH employs a public key cryptography. A public-key cryptography, also known as asymmetric cryptography, is a class of cryptographic algorithms which requires two separate keys, one of which is secret (or private) and one of which is public. 1 Together they are known as a key-pair.What does SSH public key look like?
An SSH key is an alternate way to identify yourself that doesn't require you to enter you username and password every time. SSH keys come in pairs, a public key that gets shared with services like GitHub, and a private key that is stored only on your computer. If the keys match, you're granted access.What is authorized_keys2?
ssh/authorized_keys2 file lists the DSA and RSA keys that are permitted for public key authentication (PubkeyAuthentication) in SSH protocol 2.0. The use of authorized_keys2 for protocol 2 has been deprecated since 2001.How do you create a public key?
Generating an SSH key- Open the PuTTYgen program.
- For Type of key to generate, select SSH-2 RSA.
- Click the Generate button.
- Move your mouse in the area below the progress bar.
- Type a passphrase in the Key passphrase field.
- Click the Save private key button to save the private key.
How does SSH keys work?
SSH keys are a matching set of cryptographic keys which can be used for authentication. The server then check its authorized_keys file for the public key, generate a random string and encrypts it using the public key. This encrypted message can only be decrypted with the associated private key.What does SSH Keyscan do?
ssh-keyscan is a utility for gathering the public SSH host keys of a number of hosts. It was designed to aid in building and verifying ssh_known_hosts files, the format of which is documented in sshd(8). ssh-keyscan provides a minimal interface suitable for use by shell and perl scripts.How do I clear PuTTY cache?
The way to clear putty's RSA (host) fingerprint cache.- Open the registry (start> run > regedit)
- Go to HKEY_CURRENT_USERSoftwareSimonTathamPuTTYSshHostKeys Here you will find putty's cache of host keys. The 'name' column tells you which key is for which machine.
- Delete the rows that you need .