Security Misconfiguration is simply defined as failing to implement all the security controls for a server or web application, or implementing the security controls, but doing so with errors. According to the OWASP top 10, this type of misconfiguration is number 6 on the list of critical web application security risks..
Correspondingly, what is security misconfiguration?
Security Misconfiguration arises when Security settings are defined, implemented, and maintained as defaults. Good security requires a secure configuration defined and deployed for the application, web server, database server, and platform.
Likewise, what is the impact of security misconfiguration? Impacts: Such flaws frequently give attackers unauthorized access to some system data or functionality. Occasionally, such flaws result in a complete system compromise. The business impact depends on the protection needs of the application and data.
Keeping this in consideration, which of the following are examples of security misconfiguration?
Some common security misconfigurations include:
- Unpatched systems.
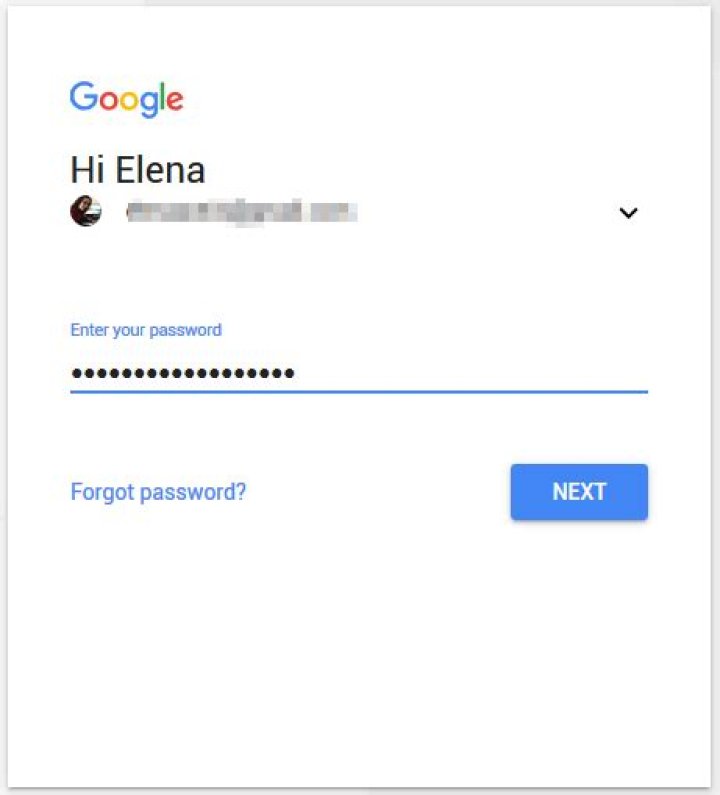
- Using default account credentials (i.e., usernames and passwords)
- Unprotected files and directories.
- Unused web pages.
- Poorly configured network devices.
What is Misconfiguration attack?
Server Misconfiguration. Server misconfiguration attacks exploit configuration weaknesses found in web and application servers. Many servers come with unnecessary default and sample files, including applications, configuration files, scripts, and webpages. Servers may include well-known default accounts and passwords.
Related Question Answers
What is Idor attack?
OWASP Top 10 explained: IDOR (Insecure Direct Object Reference) is a common vulnerability that occurs when a reference to an internal implementation object is exposed without any other access control. The vulnerability is often easy to discover and allows attackers to access unauthorized data.What is the impact of code injection vulnerability?
Injection flaws tend to be easier to discover when examining source code than via testing. Scanners and fuzzers can help find injection flaws. Injection can result in data loss or corruption, lack of accountability, or denial of access. Injection can sometimes lead to complete host takeover.What is the impact of security misconfiguration in SDLC?
Impacts: Such flaws frequently give attackers unauthorized access to some system data or functionality. Occasionally, such flaws result in a complete system compromise. The business impact depends on the protection needs of the application and data.What is broken authentication Owasp?
Simply stated, broken authentication & session management allows a cybercriminal to steal a user's login data, or forge session data, such as cookies, to gain unauthorized access to websites.What is XSS protection?
Cross-site scripting (also known as XSS) is a web security vulnerability that allows an attacker to compromise the interactions that users have with a vulnerable application. It allows an attacker to circumvent the same origin policy, which is designed to segregate different websites from each other.What is broken access control?
What is Broken Access Control? Access control enforces policy such that users cannot act outside of their intended permissions. Failures typically lead to unauthorized information disclosure, modification or destruction of all data, or performing a business function outside of the limits of the user.What is insufficient logging and monitoring?
Insufficient logging, detection, monitoring and active response occurs any time: Auditable events, such as logins, failed logins, and high-value transactions are not logged. Warnings and errors generate no, inadequate, or unclear log messages. Logs of applications and APIs are not monitored for suspicious activity.What is sensitive data exposure?
Sensitive Data Exposure occurs when an application does not adequately protect sensitive information. The data can vary and anything from passwords, session tokens, credit card data to private health data and more can be exposed.Where can security misconfigurations take place?
Security misconfiguration can happen at any level of an application stack, including the network services, platform, web server, application server, database, frameworks, custom code, and pre-installed virtual machines, containers, or storage.What is Cross Site Scripting with example?
Cross-site Scripting (XSS) is a client-side code injection attack. The web page or web application becomes a vehicle to deliver the malicious script to the user's browser. Vulnerable vehicles that are commonly used for Cross-site Scripting attacks are forums, message boards, and web pages that allow comments.Which of the following is an authorized simulated attack on a computer system?
A penetration test, colloquially known as a pen test, is an authorised simulated attack on a computer system that looks for security weaknesses, potentially gaining access to the system's features and data.What is a misconfiguration?
Security Misconfiguration is simply defined as failing to implement all the security controls for a server or web application, or implementing the security controls, but doing so with errors. According to the OWASP top 10, this type of misconfiguration is number 6 on the list of critical web application security risks.What is Owasp top10?
The OWASP Top 10 is a standard awareness document for developers and web application security. It represents a broad consensus about the most critical security risks to web applications. Globally recognized by developers as the first step towards more secure coding.What is function level access control?
Missing Function Level Access Control is one of the vulnerabilities on OWASP's Top 10 list and occurs when authentication checks in request handlers are insufficient. OWASP is a non-profit organization with the goal of improving the security of software and the internet.What is the impact of cross site scripting vulnerability?
Impacts of the Cross-site Scripting Vulnerability It ranges from user's Session Hijacking, and if used in conjunction with a social engineering attack it can also lead to disclosure of sensitive data, CSRF attacks and other security vulnerabilities.What factors contribute to sensitive data exposure attacks?
Sensitive data exposure occurs as a result of not adequately protecting a database where information is stored. This might be a result of a multitude of things such as weak encryption, no encryption, software flaws, or when someone mistakenly uploads data to an incorrect database.What is the impact of broken access control?
Once a flaw is discovered, the consequences of a flawed access control scheme can be devastating. In addition to viewing unauthorized content, an attacker might be able to change or delete content, perform unauthorized functions, or even take over site administration.Is Checkmarx open source?
Checkmarx Open Source Analysis (CxOSA) Today's software is constructed using open source components and third-party libraries, tied together with custom code. Legacy software can have potentially vulnerable or outdated open source components hiding within it, and proprietary code that must be sanitized.Which attack forces an authenticated user?
CSRF attack is an attack that occurs when a malicious website, email, or program causes a user's browser to perform an unwanted action on a trusted site for which the user is currently authenticated.