DDoS mitigation refers to the process of successfully protecting a targeted server or network from a distributed denial-of-service (DDoS) attack. By utilizing specially designed network equipment or a cloud-based protection service, a targeted victim is able to mitigate the incoming threat..
Furthermore, how does Akamai prolexic work?
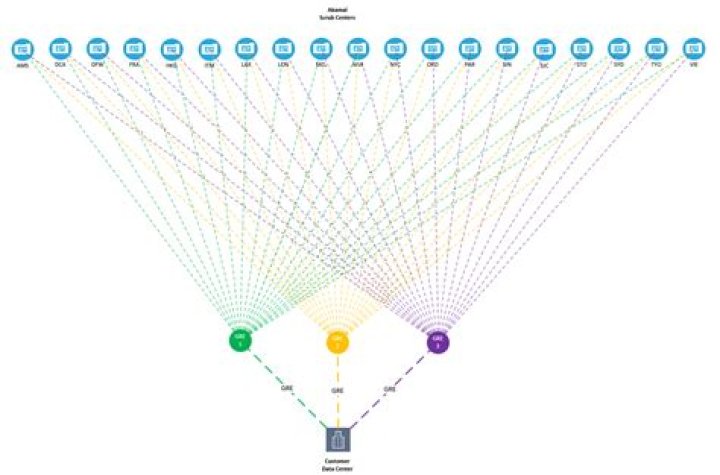
How Prolexic Routed Works. Prolexic Routed is designed to stop DDoS attacks in the cloud, before they reach your applications, data centers, and infrastructure. Network traffic is redirected through Akamai scrubbing centers by making a simple border gateway protocol (BGP) route advertisement change.
One may also ask, how does Akamai prevent DDoS? DDoS: protect your organization with Akamai Kona automatically deflects network-layer DDoS traffic and absorbs application-layer DDoS traffic at the network edge, preventing attacks from reaching the application origin.
Similarly, it is asked, what is a DDoS attack on a server?
Distributed DoS attack. A distributed denial-of-service (DDoS) attack occurs when multiple systems flood the bandwidth or resources of a targeted system, usually one or more web servers. Such an attack is often the result of multiple compromised systems (for example, a botnet) flooding the targeted system with traffic.
What is Akamai protection?
That's why the Akamai intelligent edge security platform surrounds and protects your entire architecture — core, cloud, and edge — to thwart attackers and mitigate threats wherever they emerge.
Related Question Answers
What is a bot manager?
Bot management is a feature of application security software that identifies whether a traffic request comes from a human or from a machine and then controls or blocks non-human and other suspicious requests. As such, bot management is a crucial part of modern website security.What is Akamai Kona?
AKAMAI CLOUD SECURITY SOLUTIONS: PRODUCT BRIEF. Global Cloud Platform. Built on the world's largest cloud delivery platform, Kona Site Defender extends your security infrastructure to the cloud and stops attacks before they can reach your applications.Is DDoS a virus?
Distributed DoS A distributed denial-of-service (DDoS) is a large-scale DoS attack where the perpetrator uses more than one unique IP address or machines, often from thousands of hosts infected with malware.How long do DDoS attacks last?
24 hours
Is DDoS illegal?
DDOS refers to a Distributed Denial of Service. While some observers defend DDOS attacks as a form of mass demonstration against an offending website, it is illegal under the Federal Computer Fraud and Abuse Act. Violators are subject to prison sentences of up to 10 years and a fine of up to $500,000.What is a Layer 7 attack?
An application layer DDoS attack (sometimes referred to as layer 7 DDoS attack) is a form of DDoS attack where attackers target application-layer processes. The attack over-exercises specific functions or features of a website with the intention to disable those functions or features.What is the goal of a DDoS attack?
A DoS or Denial-of-Service attack is an attack targeting the availability of web applications. Unlike other kinds of attacks, the primary goal of a DoS attack is not to steal information but to slow or take down a web site.Can you stop a DDoS attack?
But the truth is that while these steps have been effective in the past, DDoS attacks are now usually too large for these measures to be able to stop a DDoS attack completely. Again, the most you can hope for is that they will buy you a little time as a DDoS attack ramps up.Can DDoS attacks steal information?
DDoS attacks cannot steal website visitors information. The sole purpose of a DDoS attack is to overload the website resources. However, DDoS attacks can be used as a way of extortion and blackmailing. For example, website owners can be asked to pay a ransom for attackers to stop a DDoS attack.How much does a DDoS attack cost?
A DDoS attack service typically goes for $25 an hour, this means that the expected profit for crooks is around $25-$7=$18 per hour. Prices are highly variable, a DDoS attack can cost from $5 for a 300-second attack to $400 for 24 hours.What is Teardrop attack?
A teardrop attack is a denial-of-service (DoS) attack that involves sending fragmented packets to a target machine. Since the machine receiving such packets cannot reassemble them due to a bug in TCP/IP fragmentation reassembly, the packets overlap one another, crashing the target network device.What is Akamai used for?
Akamai is an organization that works towards making Internet fast, reliable and secure. It is essentially a CDN (Content Delivery Provider) provider that has multiple other internet solutions and is also, focussing largely towards internet security.Is Akamai a WAF?
Akamai's Kona Web Application Firewall is a cloud platform that effectively protects againstthese threats. Kona WAF is deployed at the edge of the network rather than the center. This means that it can identify and mitigate suspicious traffic without affecting performance or availability of the origin server.What is the best DDoS protection?
DDoS Protection Services: Our Verdict & Recommendations We found that Incapsula Enterprise, F5 Silverline DDoS Protection and Arbor Cloud offered the best protection. Imperva Incapsula's growing global network and scrubbing capacities equip it with the size needed to thwart large-scale volumetric attacks.Can firewall prevent DDoS?
Firewalls Can't Protect You from DDoS Attacks. Firewalls can't protect against complex DDoS attacks; actually, they act as DDoS entry points. Attacks pass right through open firewall ports that are intended to allow access for legitimate users.How does DDoS mitigation work?
A DDoS attack mitigation solution works by deflecting DDoS traffic in one of the outer layers – the network layer. This helps to absorb any potential application layer DDoS traffic at the network edge. This means that the threat can be prevented in the cloud before it reaches the customer origin.What is the difference between DDoS and DoS?
The Difference Between DoS and DDos Attacks The DoS attack typically uses one computer and one Internet connection to flood a targeted system or resource. The DDoS attack uses multiple computers and Internet connections to flood the targeted resource.What is Akamai Site Shield?
Site Shield cloaks websites from the public Internet, effectively removing them from Internet-accessible IP address space. This helps prevent attackers from directly targeting the application origin and forces traffic to go through the Akamai Intelligent Platform™, where attacks can be detected and mitigated.What is the difference between DDoS and DoS attack?
The Difference Between DoS and DDos Attacks The DoS attack typically uses one computer and one Internet connection to flood a targeted system or resource. The DDoS attack uses multiple computers and Internet connections to flood the targeted resource.