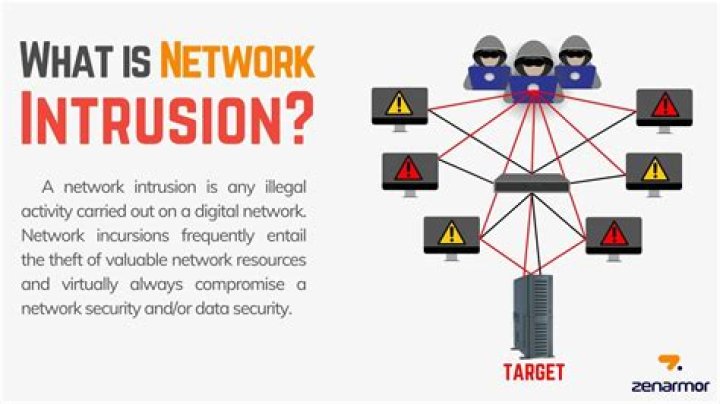
What is network intrusion?
.
Accordingly, what is network intrusion detection system?
An intrusion detection system (IDS) is a device or software application that monitors a network or systems for malicious activity or policy violations. A system that monitors important operating system files is an example of an HIDS, while a system that analyzes incoming network traffic is an example of an NIDS.
how do you prevent network intrusion? 10 Ways to Prevent Network Security Breaches in the Workplace
- Good password policy. Maintaining an unpredictable and complex password is a huge step in the right direction.
- Update regularly.
- Securing the router.
- Proper backing up of data.
- Educating the employees.
- Breach response.
- Installing centralized firewalls.
- Encrypted transmission.
Keeping this in view, what happens when a network intrusion occur?
Network Intrusion. A network intrusion refers to any unauthorized activity on a digital network. Network intrusions often involve stealing valuable network resources and almost always jeopardize the security of networks and/or their data.
What is network attack?
A network attack is an attempt to gain unauthorized access to an organization's network, with the objective of stealing data or perform other malicious activity. Passive: Attackers gain access to a network and can monitor or steal sensitive information, but without making any change to the data, leaving it intact.
Related Question AnswersWhat are the types of intrusion detection system?
For the purpose of dealing with IT, there are four main types of IDS:- Network intrusion detection system (NIDS)
- Host-based intrusion detection system (HIDS)
- Perimeter Intrusion Detection System (PIDS)
- VM based Intrusion Detection System (VMIDS)
What are the two main types of intrusion detection systems?
The two main types of intrusion detection systems are network-based and host-based. Network-based systems monitor network connections for suspicious traffic. Host-based systems reside on an individual system and monitor that system for suspicious or malicious activity.What are the benefits of intrusion detection system?
Advantages of Intrusion Detection Systems- The network or computer is constantly monitored for any invasion or attack.
- The system can be modified and changed according to needs of specific client and can help outside as well as inner threats to the system and network.
- It effectively prevents any damage to the network.
Why do we need intrusion detection systems?
Why You Need Network IDS A network intrusion detection system (NIDS) is crucial for network security because it enables you to detect and respond to malicious traffic. The primary purpose of an intrusion detection system is to ensure IT personnel is notified when an attack or network intrusion might be taking place.How do you do intrusion detection?
An IDS is either a hardware device or software application that uses known intrusion signatures to detect and analyze both inbound and outbound network traffic for abnormal activities. This is done through: System file comparisons against malware signatures. Scanning processes that detect signs of harmful patterns.What are two types of firewalls?
There are three basic types of firewalls that are used by companies to protect their data & devices to keep destructive elements out of network, viz. Packet Filters, Stateful Inspection and Proxy Server Firewalls. Let us give you a brief introduction about each of these.What intrusion detection system can do?
An IDS can be used to help analyze the quantity and types of attacks; organizations can use this information to change their security systems or implement more effective controls. An intrusion detection system can also help companies identify bugs or problems with their network device configurations.What is the difference between firewall and IDS?
The main difference being that firewall preforms actions such as blocking and filtering of traffic while and IPS/IDS detects and alert a system administrator or prevent the attack as per configuration. A firewall allows traffic based on set of rules configured.How do I harden my network?
Network hardening: Ensure your firewall is properly configured and that all rules are regularly audited; secure remote access points and users; block any unused or unneeded open network ports; disable and remove unnecessary protocols and services; implement access lists; encrypt network traffic.What is the intrusion process?
Detecting system intrusions is the process of monitoring the events occurring in a computer system or network and analyzing them for signs of possible incidents, which are violations or imminent threats of violation of computer security policies, acceptable use policies, or standard security practices.What are the phases of an attack?
The three types of attacks are reconnaissance, access, and denial of service (DoS). The first phase is defining the objective of the attack. The second phase, reconnaissance, is both a type of an attack and a phase of the attack. The third and final phase is the actual intrusion or attack on the network resources.What is unauthorized intrusion?
Unauthorized Intrusion or Hacking: Unauthorized attacks are attacks in which attacker get access in to the system by the means of different hacking or cracking techniques. This type of activity will be performed by some outsider who wants to have access of the system in order to use it for some negative purpose.What is computer security intrusion?
Computer intrusions occur when someone tries to gain access to any part of your computer system. Computer intruders or hackers typically use automated computer programs when they try to compromise a computer's security. Crash or slow down your computer.What is the number one defense against reconnaissance attacks?
Good security policies are the number one defense against reconnaissance attacks. They are discussed in more detail in Chapter 13, "Social Engineering and Physical Security."What is IPS intrusion prevention system?
An intrusion prevention system (IPS) is a form of network security that works to detect and prevent identified threats. Intrusion prevention systems continuously monitor your network, looking for possible malicious incidents and capturing information about them.Which one will not be considered in cybersecurity threat intrusion phase?
Answer to your question is Exploitation. Exploitation will not be considered in Cyber security threat Intrusion Phases. Exploitation is a part of threat attack on computer system but its more depends on geographical area. When someone try to take an advantage of a weakness in app or system that's called Exploit.What is the concept of social engineering?
Social engineering is an attack vector that relies heavily on human interaction and often involves manipulating people into breaking normal security procedures and best practices in order to gain access to systems, networks or physical locations, or for financial gain.What is security threats and its types?
There are several types of computer security threats such as Trojans, Virus, Adware, Malware, Rootkit, hackers and much more. Check some of the most harmful types of computer Security Threats.How do I protect my network security?
Preventing data breaches and other network security threats is all about hardened network protection.4. Use Network Protection Measures
- Install a firewall.
- Ensure proper access controls.
- Use IDS/IPS to track potential packet floods.
- Use network segmentation.
- Use a virtual private network (VPN)
- Conduct proper maintenance.