What is Memcached attack?
.
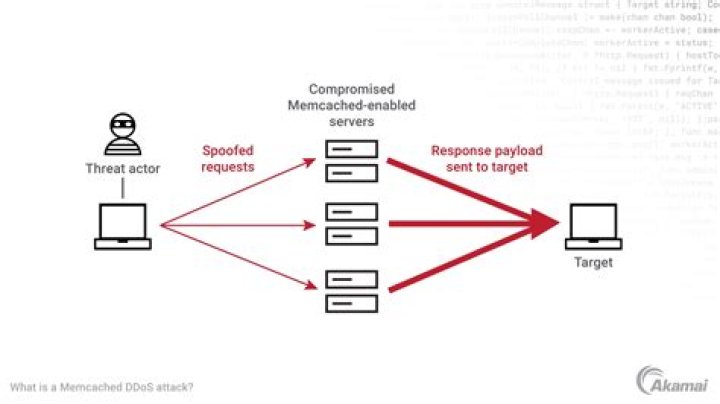
Also question is, what is a memcached DDoS attack?
A memcached distributed denial-of-service (DDoS) attack is a type of cyber attack in which an attacker attempts to overload a targeted victim with internet traffic. *Memcached is a database caching system for speeding up websites and networks.
Also Know, what is Memcrashed? Memcrashed works by exploiting the memcached program. Memcached is an open-source, high-performance, distributed, object-caching system. It's also used by many to cache their web-server-session data to speed up their sites -- and that's where the trouble starts.
Also question is, how is memcached used?
Memcached is an open source distributed memory caching system. It is used for speeding up dynamic web applications by reducing database load. Memcached stores data based on key-values for small arbitrary strings or objects including: Results of database calls.
What is a UDP reflection attack?
UDP Amplified Reflection Attacks are where the attacker uses the connection-less UDP protocol to ask a server for some piece of information, however by forging the packet header so it contains a different sender address an attacker can make it appear that the packet was sent by a different machine (In this case the
Related Question AnswersWhat are memcached servers?
Memcached servers allow applications that need to access a lot of data from an external database to cache some of the data in memory, which can be accessed much more quickly by the application than having to travel out to the database to fetch something important.How do I start memcached?
Install and configure memcached on Ubuntu- Open /etc/memcached. conf in a text editor.
- Locate the -m parameter.
- Change its value to at least 1GB.
- Locate the -l parameter.
- Change its value to 127.0.0.1 or localhost.
- Save your changes to memcached. conf and exit the text editor.
- Restart memcached. service memcached restart.
How do I connect to memcached?
To connect to a Memcached server, you need to use the telnet command on HOST and PORT names.What is memcached and how it works?
Memcached is a distributed memory caching system. It speeds up websites having large dynamic databasing by storing database object in Dynamic Memory to reduce the pressure on a server whenever an external data source requests a read. A memcached layer reduces the number of times database requests are made.What port is Memcached running on?
Confirming Memcached Installation This command shows that Memcached is running on the default port 11211. To run Memcached server on a different port, execute the command given below. This command starts the server on the TCP port 11111 and listens on the UDP port 11111 as a daemon process.How is Memcached distributed?
Unlike databases that store data on disk or SSDs, Memcached keeps its data in memory. By eliminating the need to access disks, in-memory key-value stores such as Memcached avoid seek time delays and can access data in microseconds. Memcached is also distributed, meaning that it is easy to scale out by adding new nodes.Is Memcached thread safe?
"If a highly shared cache entry stored, for example, in Memcache expires, many clients gets a cache miss. All of them will end up with setting the lock and do the cache refresh process. In other words this operations are not atomic and thus are not thread safe.How fast is Memcached?
On a fast machine with very high speed networking, memcached can easily handle 200,000+ requests per second. With heavy tuning or even faster hardware it can go many times that. Hitting it a few hundred times per second, even on a slow machine, usually isn't cause for concern.What does Flush_all 90 do?
Memcached flush_all command is used to clear all the data (i.e. key value pairs) from the Memcached server. Means, this command invalidates all existing cache items. flush_all does not pause the server, as it returns immediately.How long does memcached keep data?
30 daysWhat does Udpmix stand for?
User Datagram ProtocolWhat does Udpmix mean?
“UDP flood” is a type of Denial of Service (DoS) attack in which the attacker overwhelms random ports on the targeted host with IP packets containing UDP datagrams. As more and more UDP packets are received and answered, the system becomes overwhelmed and unresponsive to other clients.What is my port number?
All you have to do is type “netstat -a” on Command Prompt and hit the Enter button. This will populate a list of your active TCP connections. The port numbers will be shown after the IP address and the two are separated by a colon. For instance, if your IP address is something like 192.What is the best DDoS method?
Following are the methods of doing DDoS attacks:- UDP flood.
- ICMP (Ping) flood.
- SYN flood.
- Ping of Death.
- Slowloris.
- NTP Amplification.
- HTTP flood.