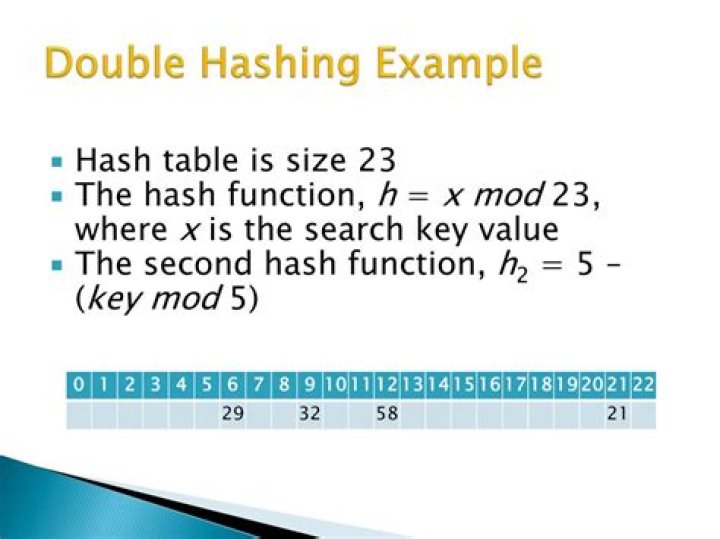
What is double hashing example?
.
Hereof, what is meant by double hashing?
Double hashing is a computer programming technique used in conjunction with open-addressing in hash tables to resolve hash collisions, by using a secondary hash of the key as an offset when a collision occurs. Double hashing with open addressing is a classical data structure on a table .
Beside above, is double hashing more secure? In general, it provides no additional security to double hash or double encrypt something. "Double Hashing" doesn't really help protect against this, since the same collisions will still result in the same first hash, which you can then MD5 again to get the second hash.
Keeping this in consideration, what is double hashing in Java?
Double Hashing is a probe sequence in which the interval between probes is computed by another hash function. Here is the source code of the Java program to implement hash tables with Double Hashing.
What is meant by hashing?
Hashing is generating a value or values from a string of text using a mathematical function. A formula generates the hash, which helps to protect the security of the transmission against tampering. Hashing is also a method of sorting key values in a database table in an efficient manner.
Related Question AnswersWhy is double hashing needed?
Why use double hashing? Double hashing is useful if an application requires a smaller hash table since it effectively finds a free slot. Although the computational cost may be high, double hashing can find the next free slot faster than the linear probing approach.Are hashes random?
Hashing is a programming technique that maps objects (such as strings) to integers. Thankfully, the worst case is typically improbable: it only happens when too many objects hash to the same value. In practice, hash functions are chosen so as to spread hash values uniformly (pseudo-randomly).What is hash table in data structure?
Hash Table is a data structure which stores data in an associative manner. In a hash table, data is stored in an array format, where each data value has its own unique index value. Thus, it becomes a data structure in which insertion and search operations are very fast irrespective of the size of the data.How do you rehash a hash table?
Rehashing of a hash map is done when the number of elements in the map reaches the maximum threshold value. When rehashing occurs a new hash function or even the same hash function could be used but the buckets at which the values are present could change.What is chaining in hashing?
Hash table. Collision resolution by chaining (closed addressing) Chaining is a possible way to resolve collisions. Each slot of the array contains a link to a singly-linked list containing key-value pairs with the same hash. List is being created, when value with the certain hash is added for the first time.What is extendible hashing in DBMS?
Definition. Extendible hashing is a dynamically updateable disk-based index structure which implements a hashing scheme utilizing a directory. The index is used to support exact match queries, i.e., find the record with a given key.What is collision in data structure?
In computer science, a collision or clash is a situation that occurs when two distinct pieces of data have the same hash value, checksum, fingerprint, or cryptographic digest. The impact of collisions depends on the application.What is separate chaining?
separate chaining. (data structure) Definition: A scheme in which each position in the hash table has a list to handle collisions. Each position may be just a link to the list (direct chaining) or may be an item and a link, essentially, the head of a list.What is hashing in Java?
Hashing is transforming a given entity (in java terms - an object) to some number (or sequence). Modren Java IDEs allow for generating good hashCode methods. Hashtable and hashmap are the same thing. They key-value pairs, where keys are hashed. Hash lists and hashsets don't store values - only keys.What is rehashing in Java?
Rehashing. Rehashing is the process of re-calculating the hashcode of already stored entries (Key-Value pairs), to move them to another bigger size hashmap when Load factor threshold is reached.What is separate chaining in data structure?
To handle collisions, the hash table has a technique known as separate chaining. Separate chaining is defined as a method by which linked lists of values are built in association with each location within the hash table when a collision occurs.What is quadratic probing in data structure?
Quadratic probing - Data Structures Quadratic probing is a scheme in computer programming for resolving collisions in hash tables. Quadratic probing operates by taking the original hash value and adding successive values of an arbitrary quadratic polynomial to the starting value.What is linear probing in hashing?
Linear probing is a scheme in computer programming for resolving collisions in hash tables, data structures for maintaining a collection of key–value pairs and looking up the value associated with a given key. Along with quadratic probing and double hashing, linear probing is a form of open addressing.Which hash function is best?
- Non-cryptographic hash functions like Murmur3, Cityhash and Spooky are pretty close together.
- MD5 seems to be a good tradeoff when using cryptographic hash functions, although SHA256 may be more secure to the collision vulnerabilities of MD5 and SHA1.