What is DoS attack in computer?

.
Just so, what does DoS attack mean?
A denial-of-service (DoS) is any type of attack where the attackers (hackers) attempt to prevent legitimate users from accessing the service. In a DoS attack, the attacker usually sends excessive messages asking the network or server to authenticate requests that have invalid return addresses.
Likewise, how is a DoS attack performed? A Denial-of-Service (DoS) attack is an attack meant to shut down a machine or network, making it inaccessible to its intended users. DoS attacks accomplish this by flooding the target with traffic, or sending it information that triggers a crash.
Consequently, what is DoS attack and its types?
Broadly speaking, DoS and DDoS attacks can be divided into three types: Volume Based Attacks. Includes UDP floods, ICMP floods, and other spoofed-packet floods. The attack's goal is to saturate the bandwidth of the attacked site, and magnitude is measured in bits per second (Bps).
What is difference between DoS and DDoS attack?
The Difference Between DoS and DDos Attacks The DoS attack typically uses one computer and one Internet connection to flood a targeted system or resource. The DDoS attack uses multiple computers and Internet connections to flood the targeted resource.
Related Question AnswersHow can we prevent DoS attacks?
Six steps to prevent DDoS attacks- Buy more bandwidth.
- Build redundancy into your infrastructure.
- Configure your network hardware against DDoS attacks.
- Deploy anti-DDoS hardware and software modules.
- Deploy a DDoS protection appliance.
- Protect your DNS servers.
What is the goal of a DoS attack?
Unlike other kinds of attacks, the primary goal of a DoS attack is not to steal information but to slow or take down a web site. The attackers' motivations are diverse, ranging from simple fun, to financial gain and ideology ( hacktivism ).How do you detect DoS attacks?
The best way to detect and identify a DoS attack would be via network traffic monitoring and analysis. Network traffic can be monitored via a firewall or intrusion detection system.Is DoS attack illegal?
DDOS refers to a Distributed Denial of Service. While some observers defend DDOS attacks as a form of mass demonstration against an offending website, it is illegal under the Federal Computer Fraud and Abuse Act. Violators are subject to prison sentences of up to 10 years and a fine of up to $500,000.Can you trace a DDOS attack?
People using a tool to conduct distributed denial-of-service (DDOS) attacks against other websites in support of WikiLeaks can easily be traced, according to computer security researchers.What is DoS protection on my router?
Enable DoS protection feature can filter suspicious or unreasonable packets to prevent from flooding the network with large amounts of fake traffic. ASUS router uses following methods to detect suspicious attack.What is Teardrop attack?
A teardrop attack is a denial-of-service (DoS) attack that involves sending fragmented packets to a target machine. Since the machine receiving such packets cannot reassemble them due to a bug in TCP/IP fragmentation reassembly, the packets overlap one another, crashing the target network device.Is a common indicator of a DoS attack?
Indicators of a DoS attack include: Atypically slow network performance such as long load times for files or websites. The inability to load a particular website such as your web property. A sudden loss of connectivity across devices on the same network.What do you mean by DoS attack?
In computing, a denial-of-service attack (DoS attack) is a cyber-attack in which the perpetrator seeks to make a machine or network resource unavailable to its intended users by temporarily or indefinitely disrupting services of a host connected to the Internet.What is botnet attack?
A botnet is a collection of internet-connected devices infected by malware that allow hackers to control them. Cyber criminals use botnets to instigate botnet attacks, which include malicious activities such as credentials leaks, unauthorized access, data theft and DDoS attacks.What are password attacks?
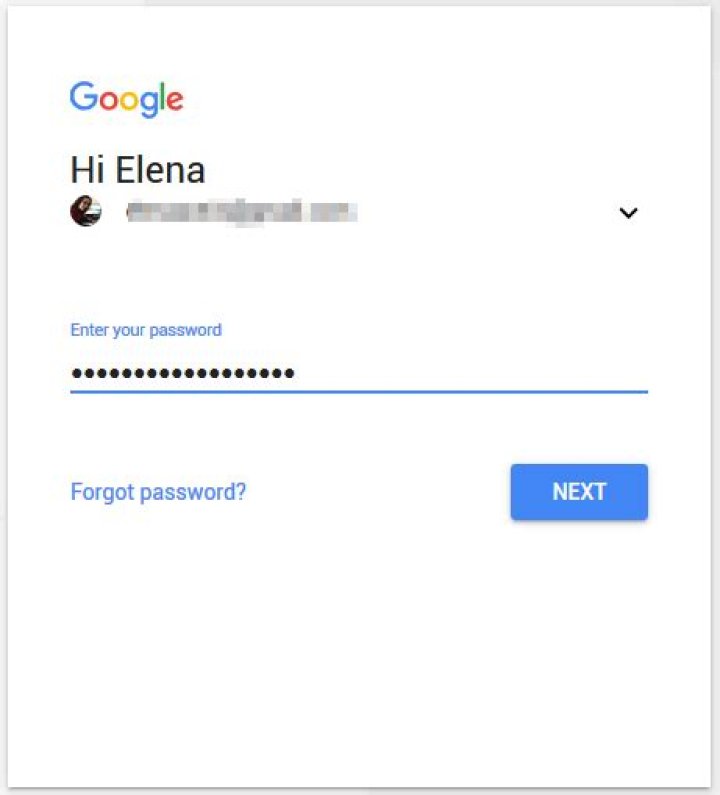
An attack that takes advantage of the fact people tend to use common words and short passwords. The hacker uses a list of common words, the dictionary, and tries them, often with numbers before and/or after the words, against accounts in a company for each username.What is the best DDoS method?
Following are the methods of doing DDoS attacks:- UDP flood.
- ICMP (Ping) flood.
- SYN flood.
- Ping of Death.
- Slowloris.
- NTP Amplification.
- HTTP flood.