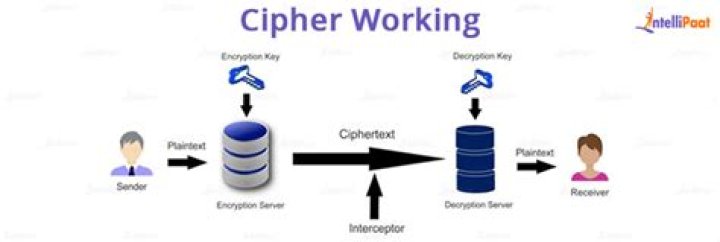
In cryptography, a cipher (orcypher) is an algorithm for performing encryption ordecryption—a series of well-defined steps that can befollowed as a procedure. When using a cipher the originalinformation is known as plaintext, and the encrypted form asciphertext..
Furthermore, what is the use of ciphers?
In cryptology, the discipline concerned with the studyof cryptographic algorithms, a cipher is an algorithm forencrypting and decrypting data. Many communication technologies,including phones, digital television and ATMs, rely onciphers to maintain security and privacy.
Likewise, what is the difference between a cipher and a code? The difference between a cipher and a code is: acipher changes a message on a letter-by-letter basis, whilea code converts whole plaintext words or phrases into otherwords or numbers. The Rossignols' Great Cypher was used by LouisXIV of France in the 1600s and was an example of anomenclator.
Hereof, what are the types of ciphers?
Cipher Types
- AMSCO (period times 8-12 lines deep)
- AUTOKEY (40-55 letters)
- BACONIAN (25-letter plaintext maximum)
- BAZERIES (150-250 letters)
- BEAUFORT (width of period times 10-15 lines deep)
- BIFID (125-150 letters)
- CADENUS (period not over 6)
- CHECKERBOARD (60-90 pairs)
What is tls_ecdhe_rsa_with_aes_128_gcm_sha256?
Client-server encryption technique explanation(TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256, 128 bit keys)TLS_ECDHE means ephemeral Elliptic Curve Diffie-Hellman and asWikipedia says it allows two parties to establish a shared secretover an insecure channel.
Related Question Answers
How does cipher work?
“Cipher” means “If this spellis represented by a card, you may exile this card encoded on acreature you control” and “For as long as this card isencoded on that creature, that creature has 'Whenever this creaturedeals combat damage to a player, you may copy the encoded card andyou may cast the copy without payingWhat is TLS 1.2 used for?
TLS stands for Transport Layer Security which isa cryptographic protocol used to increase security overcomputer networks. TLS 1.1 - Released in 2006 and publishedas RFC 4346. TLS 1.2 - Released in 2008 and published as RFC5246. TLS 1.3 - As of January 2016 this version ofTLS is in working draft.How do you solve ciphers?
Steps - Understand the way a cryptogram works. Most cryptograms orcryptoquotes are basic substitution ciphers, meaning that theletters of the alphabet are being represented by otherletters.
- Solve one letter at a time.
- Make the best guess, then guess again.
- Work in pencil.
- Embrace your mistakes.
What is a cipher character?
Sometimes a "cipher of a character" meansthat the character is very similar to the author in manyways. By (one possible) definition, a cipher is acharacter/symbol that, when standing by itself, meansnothing, but, when included as part of a code, suddenly obtainsmeaning.What is a weak cipher?
Weak Cipher Definition. A weak cipher isdefined as an encryption/decryption algorithm that uses a key ofinsufficient length. Using an insufficient length for a key in anencryption/decryption algorithm opens up the possibility (orprobability) that the encryption scheme could be broken (i.e.cracked).What is cypher key?
Cypher Keys and Fragments These keys are used at the Premium Vendor to getEncrypted Caches, which give the player 3 random cosmetic items.Cypher Keys may be acquired by purchasing them with PremiumCredits. Encrypted Caches have a chance of dropping duplicateitems.What is meant by decryption?
Definition of 'Decryption'Definition: The conversion of encrypted data into itsoriginal form is called Decryption. It is generally areverse process of encryption. It decodes the encrypted informationso that an authorized user can only decrypt the data becausedecryption requires a secret key or password.What encryption means?
The translation of data into a secret code.Encryption is the most effective way to achieve datasecurity. To read an encrypted file, you must have access toa secret key or password that enables you to decrypt it.Unencrypted data is called plain text ; encrypted data isreferred to as cipher text.What is the oldest cipher?
The earliest known use of cryptography isfound in non-standard hieroglyphs carved into the wall of a tombfrom the Old Kingdom of Egypt circa 1900 BC.What is Monoalphabetic Cipher example?
A monoalphabetic substitution is a cipherin which each occurrence of a plaintext symbol is replaced by acorresponding ciphertext symbol to generateciphertext. Example: An affine cipher E(x)=(ax+ b) MOD 26 is an example of a monoalphabeticsubstitution.What is homophonic cipher?
The Homophonic Substitution cipher is asubstitution cipher in which single plaintext letters can bereplaced by any of several different ciphertext letters.They are generally much more difficult to break than standardsubstitution ciphers.What is Playfair cipher example?
The Playfair cipher encrypts pairs of letters(digraphs), instead of single letters as is the case with simplersubstitution ciphers such as the Caesar Cipher.Frequency analysis is still possible on the Playfair cipher,however it would be against 600 possible pairs of letters insteadof 26 different possible letters.What is Monoalphabetic cipher with example?
Monoalphabetic cipher is a substitutioncipher in which for a given key, the cipher alphabet foreach plain alphabet is fixed throughout the encryption process. Forexample, if 'A' is encrypted as 'D', for any number ofoccurrence in that plaintext, 'A' will always get encrypted to'D'.How does Vernam cipher work?
The Vernam Cipher is based on the principle thateach plaintext character from a message is 'mixed' with onecharacter from a key stream. If a truly random key stream is used,the result will be a truly 'random' ciphertext which bearsno relation to the original plaintext.What is meant by hashing?
Hashing is generating a value or values from astring of text using a mathematical function. A formula generatesthe hash, which helps to protect the security of thetransmission against tampering. Hashing is also a method ofsorting key values in a database table in an efficientmanner.Why do we use ciphers?
A cipher enables private communication andis often used in email, so that if an encryptedmessage is intercepted by an unauthorized user, the messagecannot be read. A block cipher encrypts plaintext with a keyand algorithm, which affects a complete block of data containingseveral bits.What are codes?
A code is an organized system of signs.Codes are the rules and conventions about how you combinesigns, how signs relate to each other. (Remember that signs can bewords or images, but also behaviors, or concepts such asmetaphors.) 4 x 9 = 36. Language is a code.Is Morse code a cipher?
One of the most famous examples of a cipher inregular use is Morse Code (which is not a code, butrather a cipher). Morse Code has the benefit that itcan be transmitted in several ways, such as written, by sound or bylight. Each letter is replaced by a series of dots and dashes asgiven by the key below.What is a modern cipher suite?
A cipher suite is a set of algorithms that helpsecure a network connection that uses Transport Layer Security(TLS) or its now-deprecated predecessor Secure Socket Layer (SSL).In addition, cipher suites can include signatures and anauthentication algorithm to help authenticate the server and orclient.