news /
What is audit logging in Linux?
The Linux Audit framework is a kernel feature (paired with userspace tools) that can log system calls. For example, opening a file, killing a process or creating a network connection. These audit logs can be used to monitor systems for suspicious activity.
.
Also to know is, what is auditing and logging?
An audit log is a document that records an event in an information (IT) technology system. In addition to documenting what resources were accessed, audit log entries usually include destination and source addresses, a timestamp and user login information.
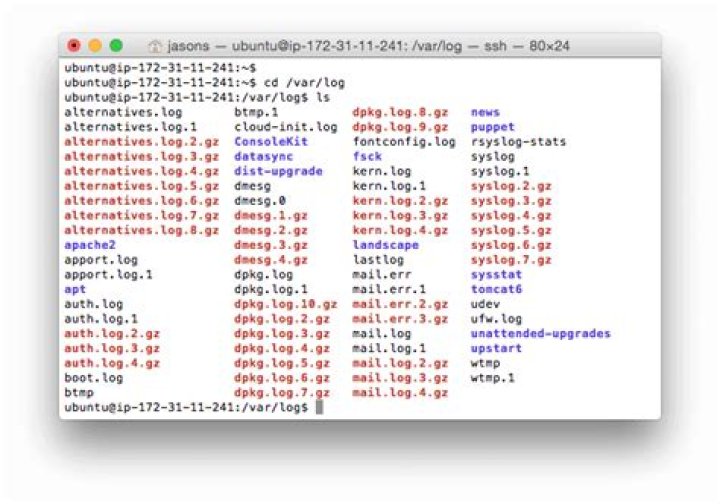
Beside above, where are audit logs stored in Linux? By default, the Audit system stores log entries in the /var/log/audit/audit. log file; if log rotation is enabled, rotated audit. log files are stored in the same directory.
Also Know, how do I audit in Linux?
How to Audit File Access on Linux
- -w: specify the file you want to audit/watch.
- -p: which operation/permission you want to audit/watch, r for read, w for write, x for execute, a for append.
- -k: specify a keyword for this audit rule, when searching the audit log, you can search by this keyword.
How do I find audit logs?
Use the EAC to view the administrator audit log
- In the EAC, go to Compliance management > Auditing, and choose Run the admin audit log report.
- Choose a Start date and End date, and then choose Search.
- If you want to print a specific audit log entry, choose the Print button in the details pane.
What is the use of log files?
LOG is the file extension for an automatically produced file that contains a record of events from certain software and operating systems. While they can contain a number of things, log files are often used to show all events associated with the system or application that created them.What are the logging policies?
1 Answer. A logging policy states what types of activities your application should track. Basically, your policy should state what types of actions need to be logged in order to trace potential fraud, inappropriate use, etc.What is the system log?
By Vangie Beal The system log file contains events that are logged by the operating system components. These events are often predetermined by the operating system itself. System log files may contain information about device changes, device drivers, system changes, events, operations and more.What is the purpose of audit trails?
An audit trail is a step-by-step record by which accounting or trade data can be traced to its source. Audit trails are used to verify and track many types of transactions including accounting transactions and trades in brokerage accounts.What is the application log?
An application log is a file of events that are logged by a software application. It contains errors, informational events and warnings. The format and content of an application log are determined by the developer of the software program, rather than the OS.Why are audit logs important?
Having detailed audit logs helps companies monitor data and keep track of potential security breaches or internal misuses of information. They help to ensure users follow all documented protocols and also assist in preventing and tracking down fraud.What is audit system?
System audit is defined as “A systematic and independent examination to determine whether activities and related results comply with planned arrangements and whether these arrangements are implemented effectively and are suitable to achieve objectives.”How do you audit a file?
To enable file auditing on a file or folder in Windows:- Locate the file or folder you want to audit in Windows Explorer.
- Right-click the file or folder and then click Properties.
- Click the Security tab.
- Click Advanced.
- Click the Auditing tab.
- If you are using Windows Server 2008, click Edit.
- Click Add.
What are audit rules?
audit. rules is a file containing audit rules that will be loaded by the audit daemon's init script whenever the daemon is started. The auditctl program is used by the initscripts to perform this operation.What is Auditctl?
Description. The auditctl program is used to control the behavior, get status, and add or delete rules into the 2.6 kernel's audit system.What does SELinux mean?
As part of the Android security model, Android uses Security-Enhanced Linux (SELinux) to enforce mandatory access control (MAC) over all processes, even processes running with root/superuser privileges (Linux capabilities). SELinux operates on the principle of default denial: Anything not explicitly allowed is denied.How do you access logs?
Find or View Log Files- Log on to the Web server computer as Administrator.
- Click Start, point to Settings, and then click Control Panel.
- Double-click Administrative Tools, and then double-click Internet Services Manager.
- Select the Web site from the list of different served sites in the pane on the left.



