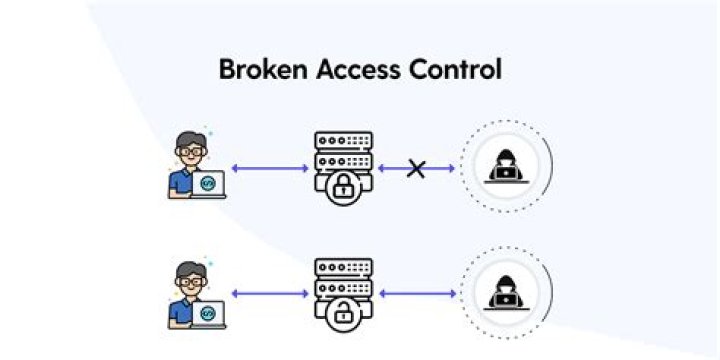
Common Access Control Vulnerabilities Not restricting the others from viewing or modifying someone else's record or account. Privilege escalation- Acting as an administrator when logged in as another user. Metadata manipulation with tampering or replaying to elevate privileges..
Just so, what is the impact of broken access control?
Once a flaw is discovered, the consequences of a flawed access control scheme can be devastating. In addition to viewing unauthorized content, an attacker might be able to change or delete content, perform unauthorized functions, or even take over site administration.
what does access control do? The goal of access control is to minimize the risk of unauthorized access to physical and logical systems. Access control is a fundamental component of security compliance programs that ensures security technology and access control policies are in place to protect confidential information, such as customer data.
In this manner, what is broken access control attack?
Access control enforces policy such that users cannot act outside of their intended permissions. Failures typically lead to unauthorized information disclosure, modification or destruction of all data, or performing a business function outside of the limits of the user.
What is broken authentication?
These types of weaknesses can allow an attacker to either capture or bypass the authentication methods that are used by a web application. Permits automated attacks such as credential stuffing, where the attacker has a list of valid usernames and passwords.
Related Question Answers
What is the process of authentication?
The process of identifying an individual, usually based on a username and password. In security systems, authentication is distinct from authorization , which is the process of giving individuals access to system objects based on their identity.What is the impact of broken authentication and session management?
Broken Authentication Vulnerability. Application functions related to authentication and session management are often not implemented correctly, allowing attackers to compromise passwords, keys, or session tokens, or to exploit other implementation flaws to assume other users' identities.What is improper access control?
The Improper Access Control weakness describes a case where software fails to restrict access to an object properly.What is the impact of code injection vulnerability?
Scanners and fuzzers can help find injection flaws. Injection can result in data loss or corruption, lack of accountability, or denial of access. Injection can sometimes lead to complete host takeover. Certain types of code injection are errors in interpretation, giving special meaning to user input.What is sensitive data exposure?
Sensitive Data Exposure occurs when an application does not adequately protect sensitive information. The data can vary and anything from passwords, session tokens, credit card data to private health data and more can be exposed.What is server misconfiguration?
Server Misconfiguration. Server misconfiguration attacks exploit configuration weaknesses found in web and application servers. Servers may include well-known default accounts and passwords. Failure to fully lock down or harden the server can leave improperly set file and directory permissions.What is insufficient attack protection?
Insufficient Attack Protection refers to the inability to detect, prevent and respond to various kinds of attacks against the application as a whole.What is API security testing?
It is important for an organization to identify the threats to secure data from any kind of risk. That's why API security testing is very important. An Application Programming Interface provides the easiest access point to hackers. An API is a user interface intended for different users.What is the purpose of Owasp?
OWASP (Open Web Application Security Project) is an organization that provides unbiased and practical, cost-effective information about computer and Internet applications.What factors contribute to sensitive data exposure attacks?
Banking account numbers, credit card numbers, healthcare data, session tokens, Social Security number, home address, phone numbers, dates of birth, and user account information such as usernames and passwords are some of the types of information that can be left exposed.What is XSS vulnerability?
Cross-site scripting (XSS) is a type of computer security vulnerability typically found in web applications. XSS enables attackers to inject client-side scripts into web pages viewed by other users. A cross-site scripting vulnerability may be used by attackers to bypass access controls such as the same-origin policy.What is Owasp top10?
The OWASP Top 10 is a powerful awareness document for web application security. It represents a broad consensus about the most critical security risks to web applications. Project members include a variety of security experts from around the world who have shared their expertise to produce this list.How many types of access are there?
Three Types of Access Control Three access control paradigms organize how people gain access: role-based access control (RBAC), discretionary access control (DAC), and mandatory access control (MAC).What is the main purpose of access control?
Access control systems may also be used to control access into certain areas located within the interior of buildings. The purpose of an access control system is to provide quick, convenient access to those persons who are authorized, while at the same time, restricting access to unauthorized people.What is access control models?
Access control models have four flavors: Mandatory Access Control (MAC), Role Based Access Control (RBAC), Discretionary Access Control (DAC), and Rule Based Access Control (RBAC or RB-RBAC). The Mandatory Access Control, or MAC, model gives only the owner and custodian management of the access controls.What is the most common form of physical access control?
The most common physical access controls are used at hospitals, police stations, government offices, data centers, and any area that contains sensitive equipment and/or data.What is the benefit of role based access control?
Benefits of RBAC With hundreds or thousands of employees, security is more easily maintained by limiting unnecessary access to sensitive information based on each user's established role within the organization. Other advantages include: Reducing administrative work and IT support.What are the four elements of an access control system?
There are four main elements of an access control system: 1. Access control barrier; 2. Access control verification or identification equipment; 3.