Application Protocol. Application protocols govern various processes, such as the process for downloading a web page, or for sending e-mail. The application protocol directs how these processes are done..
Furthermore, what are application level protocols?
Application Level Protocols. Networks build their various communication protocols on top of each other. While IP allows a computer to communicate across a network, it misses various features which TCP adds. SMTP, the protocol used for sending email, is the workhorse protocol built on TCP/IP.
One may also ask, what is application level? The application level refers to the applications that sit on top of the network and use the networks to get their data from one endpoint to another—such as a server.
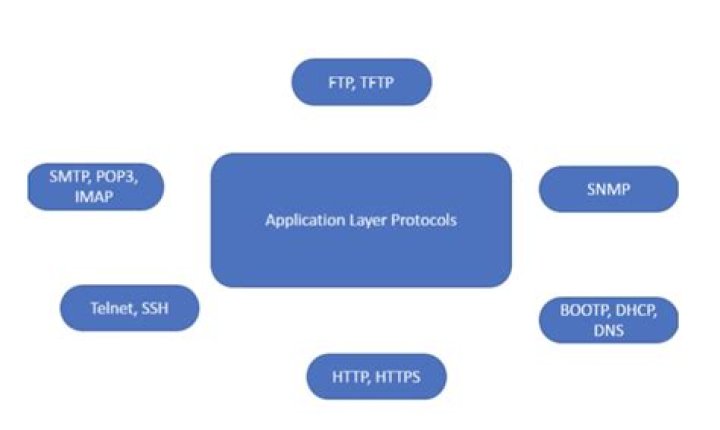
Subsequently, question is, what are the different application layer protocols?
Application Layer protocol:-
- TELNET: Telnet stands for the TELecomunications NETwork.
- FTP: FTP stands for file transfer protocol.
- TFTP:
- NFS:
- SMTP:
- LPD:
- X window:
- SNMP:
What layer is HTTP?
application layer
Related Question Answers
Is DNS an application layer protocol?
Protocols at the Physical, Data-Link, Network, or Transport layers do not use names. Only applications need to use names, so DNS is an application-layer protocol because it allows the application to translate a name into a network address.What layer is FTP?
application layer
Is http an application layer protocol?
HyperText Transfer Protocol (HTTP) The HyperText Transfer Protocol, or HTTP, must be the most widely used Application layer protocol in the world today. Each time you open a Web browser to surf the Internet, you are using HTTP over TCP/IP.Is DHCP an application layer protocol?
DHCP runs at the application layer of the Transmission Control Protocol/IP (TCP/IP) stack to dynamically assign IP addresses to DHCP clients and to allocate TCP/IP configuration information to DHCP clients. This includes subnet mask information, default gateway IP addresses and domain name system (DNS) addresses.Is SSH an application layer protocol?
SSH, is an OSI model application layer protocol use cryptographic to allow remote login and other network services to operate securely over an unsecured network. SSL runs inside TCP and encrypts the data inside the TCP packets. IPsec replaces IP with an encrypted version of the IP layer.What layer is SMTP?
application layer
What does application layer do?
The application layer is a layer in the Open Systems Interconnection (OSI) seven-layer model and in the TCP/IP protocol suite. It consists of protocols that focus on process-to-process communication across an IP network and provides a firm communication interface and end-user services.Is DNS a protocol?
(Although many people think "DNS" stands for "Domain Name Server," it really stands for "Domain Name System.") DNS is a protocol within the set of standards for how computers exchange data on the internet and on many private networks, known as the TCP/IP protocol suite.What is application layer message?
Application layer messages (data) All messages sent in a network pass through each of the network layers. Finally, the term message denotes an information unit whose source and destination entity exists above the network layer (i.e, application layer).What is Session Layer protocol?
The session layer provides the mechanism for opening, closing and managing a session between end-user application processes, i.e., a semi-permanent dialogue. An example of a session-layer protocol is the OSI protocol suite session-layer protocol, also known as X. 225 or ISO 8327.What is TCP and UDP?
They are TCP or Transmission Control Protocol and UDP or User Datagram Protocol. TCP is connection oriented – once a connection is established, data can be sent bidirectional. UDP is a simpler, connectionless Internet protocol. Multiple messages are sent as packets in chunks using UDP.Is OSI model a protocol?
The Open System Interconnection (OSI) model defines a networking framework to implement protocols in seven layers. There is really nothing to the OSI model. In fact, it's not even tangible. The OSI model doesn't perform any functions in the networking process.What are the four things defined in an application layer protocol?
a) An application layer protocol typically defines four things. What are these four things? Types of messages, syntax of messages, semantics of messages, and timing (when and how).What is FTP and HTTP?
HTTP and FTP both are the file transfer protocols that are used to transfer data between client and server. The basic point that distinguishes HTTP and FTP is that HTTP on request provides a web page from a web server to web browser. On another side, FTP is used to upload or download file between client and server.Which is not application layer protocol?
Which is not a application layer protocol? Explanation: TCP is transport layer protocol. Explanation: For Application, Presentation and Session layers there is no data format for message.What is an application question?
Application questions consist of a subject and a question—basically, they're just like an email. They have three statuses: Awaiting applicant response: You're waiting to hear back from the applicant. Solved: The question has been answered or you've come to some other resolution of the issue.Is Telnet an application layer protocol?
TELNET is client-server application that allows a user to log onto remote machine and lets the user to access any application program on a remote computer. TELNET uses the NVT (Network Virtual Terminal) system to encode characters on the local system. Many application protocols are built upon the TELNET protocol.What is application layer in TCP IP?
In TCP/IP, the application layer contains the communications protocols and interface methods used in process-to-process communications across an Internet Protocol (IP) computer network. The OSI model defines the application layer as the user interface responsible for displaying received information to the user.What is Application Layer Security?
Application layer security refers to ways of protecting web applications at the application layer (layer 7 of the OSI model) from malicious attacks. Since the application layer is the closest layer to the end user, it provides hackers with the largest threat surface.