How is authentication done?

.
Beside this, what is authentication process?
Definition: Authentication is the process of recognizing a user's identity. Authentication process can be described in two distinct phases - identification and actual authentication. Identification phase provides a user identity to the security system. This identity is provided in the form of a user ID.
Secondly, what is the best way to authenticate users?
- Passwords. One of the most widespread and well-known methods of authentication are passwords.
- Two-Factor Authentication.
- Captcha Test.
- Biometric Authentication.
- Authentication and Machine Learning.
- Public and Private Key-pairs.
- The Bottom Line.
Likewise, people ask, what are three methods for authentication?
There are generally three recognized types of authentication factors:
- Type 1 – Something You Know – includes passwords, PINs, combinations, code words, or secret handshakes.
- Type 2 – Something You Have – includes all items that are physical objects, such as keys, smart phones, smart cards, USB drives, and token devices.
Is a password authentication or Authorisation?
Authentication is the process of verifying who you are. When you log on to a PC with a user name and password you are authenticating. Authorization is the process of verifying that you have access to something.
Related Question AnswersWhy is authentication needed?
The error may simply be a sign-in issue, which sometimes occurs when the Play Store is updated. The first trick is to go into your phone's main Settings menu and then Accounts and simply remove the Google account you have registered (the one that's getting the “authentication is required” message).What is the purpose of authentication?
Authentication is important because it enables organizations to keep their networks secure by permitting only authenticated users (or processes) to access its protected resources, which may include computer systems, networks, databases, websites and other network-based applications or services.What are different types of authentication?
What are the different types of authentication methods?- Single Factor Authentication. Also known as primary authentication, this is the simplest and most common form of authentication.
- 2nd Factor Authentication.
- Multi-Factor Authentication.
- Authentication Method Protocols.
- HTTP Basic Auth.
- API Keys.
- OAuth.
What do u mean by authentication?
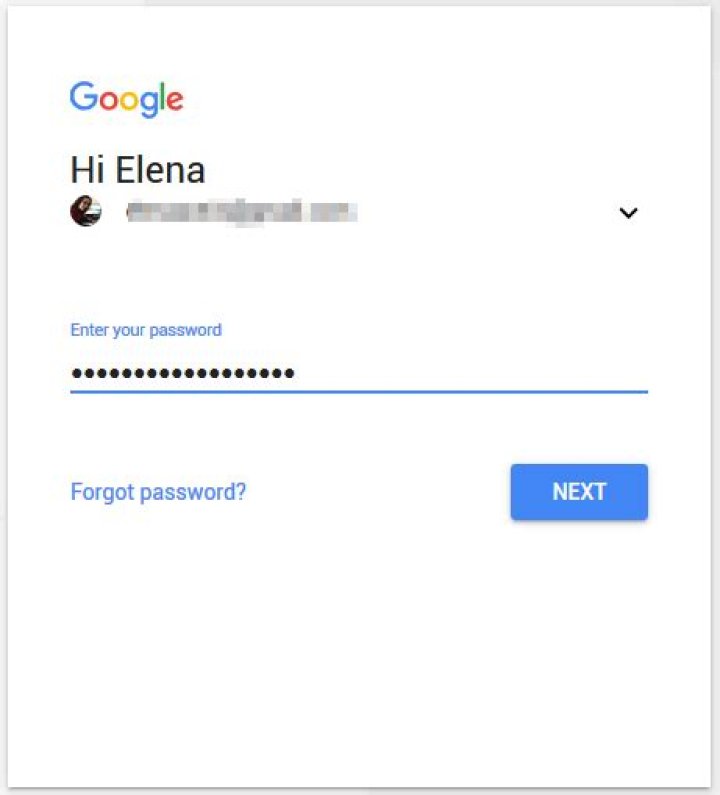
Authentication. In computing, authentication is the process of verifying the identity of a person or device. A common example is entering a username and password when you log in to a website. Biometrics may also be used for authentication.What is authentication application?
What is an authentication app? Authentication apps generate security codes for signing in to sites that require a high level of security. You can use these apps to get security codes even if you don't have an internet connection or mobile service.What is difference between authorization and authentication?
Difference between Authentication and Authorization. Authentication means confirming your own identity, while authorization means granting access to the system. In simple terms, authentication is the process of verifying who you are, while authorization is the process of verifying what you have access to.What is HTTP basic authentication and how it works?
HTTP basic authentication is a simple challenge and response mechanism with which a server can request authentication information (a user ID and password) from a client. The client passes the authentication information to the server in an Authorization header. The authentication information is in base-64 encoding.What is the most common form of authentication?
Passwords are the most common form of authentication.What is the best authentication method?
- Passwords. One of the most widespread and well-known methods of authentication are passwords.
- Two-Factor Authentication.
- Captcha Test.
- Biometric Authentication.
- Authentication and Machine Learning.
- Public and Private Key-pairs.
- The Bottom Line.
What is authentication used for?
Authentication is used by a server when the server needs to know exactly who is accessing their information or site. Authentication is used by a client when the client needs to know that the server is system it claims to be. In authentication, the user or computer has to prove its identity to the server or client.What are three examples of two factor authentication?
Examples of Two Factor Authentication Posession factors like your credit card include (but are not limited to) a physical key, fob, and personal cell phones.Which authentication method is the most secure?
biometric authenticationWhat are the types of two factor authentication?
The Different Forms of Two-Factor Authentication: SMS, Autheticator Apps, and More- SMS Verification. RELATED: What Is Two-Factor Authentication, and Why Do I Need It?
- App-Generated Codes (Like Google Authenticator and Authy)
- Physical Authentication Keys.
- App-Based Authentication.