Can Botnets be used for good?
.
People also ask, what can Botnets be used for?
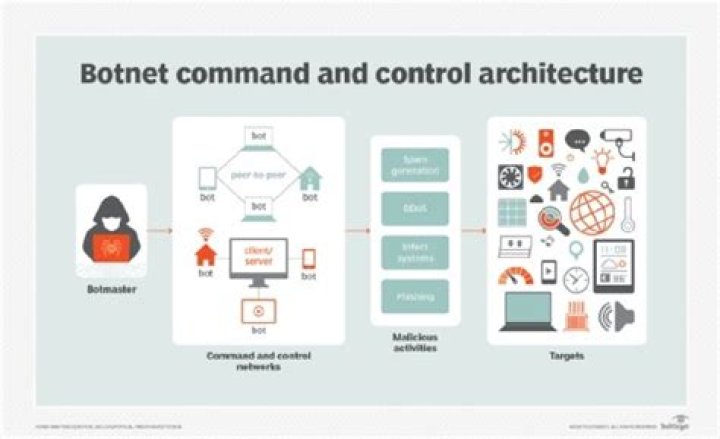
A botnet is a number of Internet-connecteddevices, each of which is running one or more bots. Botnetscan be used to perform distributed denial-of-serviceattack (DDoS attack), steal data, send spam, and allows theattacker to access the device and its connection.
Also Know, is it illegal to have a botnet? A botnet is used for illegal/maliciouspurposes, if so, then it is illegal and is bound bylaw. However, if the botnet has every single personconsent in that network. A botnet will be designated for agood deed.
Subsequently, one may also ask, what is the best botnet?
Here we count down five botnets that emerged in2017:
- 1. ' Star Wars' Twitter Botnet.
- Hajime Malware Botnet.
- WireX Android Botnet.
- The Reaper IoT Botnet.
- Satori IoT Botnet.
What are some real world examples of botnets?
Smaller botnets can be in the hundreds orlow thousands of infected machines, and larger ones can run intothe millions of PCs. Examples of well-knownbotnets that have emerged in recent years include Conficker,Zeus, Waledac, Mariposa and Kelihos.
Related Question AnswersWhat is zombie attack?
A zombie (also known as a bot) is a computer thata remote attacker has accessed and set up to forward transmissions(including spam and viruses) to other computers on the Internet.The increasing prevalence of high speed connections makes homecomputers appealing targets for attack.What is the primary goal of a DoS attack?
A DoS or Denial-of-Service attack is anattack targeting the availability of web applications.Unlike other kinds of attacks, the primary goal of a DoSattack is not to steal information but to slow or take down aweb site.Can malware affect WIFI?
There have been reports for years about routers beinginfected with malware. Once the malware has infecteda device connected to the network, it can then infectyour router and spread the malware to all devices that areconnected to the Wi-Fi network.How do botnets work?
The strategy typically requires users to infect theirown systems by opening email attachments, clicking on malicious popup ads, or downloading dangerous software from a website. Afterinfecting devices, botnets are then free to access andmodify personal information, attack other computers, and commitother crimes.How do botnets communicate?
Typically these type of botnet communicatesthrough Internet Relay Chat(IRC). These clients communicatewith chat servers to transfer messages to other clients. IRCnetworks use simple, low bandwidth communication methods,making them widely used to host botnets.How a Botnet can be created?
Botnets are created by infecting multiplesystems with malware (malicious software) and thus rendering themto be slave systems to the botnet operator. This malwarecan be introduced to a computer system in various forms, forexample: A trojan within an email attachment. Drive-bydownloads.How can botnets affect you?
As you are aware, a single piece of malwarecan cause enormous damage. Now imagine what an army ofmillions of computers can do through coordinated attacks.Even small botnets can affect a business. And the worst partis that your computer can be recruited into a botnetas easy as 1-2-3.How much does a botnet cost?
This means the actual cost of an attack using abotnet of 1000 workstations can amount to $7 per hour. Theasking prices for the services we managed to find were, onaverage, $25 per hour, meaning the cybercriminals organizingDDoS attack are making a profit of about $18 for every hour of anattack.How can Botnets be prevented?
Ways to prevent botnet malware:- Install trusted, powerful antivirus software on yourcomputer.
- Set your software settings to update automatically.
- Be careful what you click, download, or open.